Table of Contents
Initial Exploitation of Critical Confluence Vulnerability
Threat intelligence firm GreyNoise recently observed the first in-the-wild exploitation attempts targeting a critical vulnerability in Atlassian Confluence Data Center and Confluence Server. This exploitation comes on the heels of a patch issued to address the vulnerability, which is an improper authorization flaw tracked as CVE-2023-22518. This security defect has a CVSS score of 9.1 and can lead to significant data loss across all Confluence versions.
Threat Actors Targeting Global Organizations
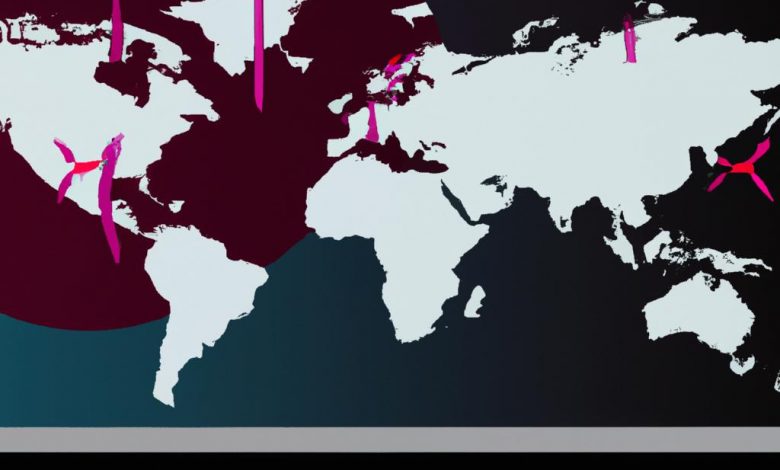
GreyNoise's scanners detected the exploitation of the vulnerability over the weekend, with targets including organizations in the US, Taiwan, Ukraine, Georgia, Latvia, and Moldova. Attacks were originating from three different IP addresses, as indicated by GreyNoise CEO and founder Andrew Morris.
Details on CVE-2023-22518: The Critical Security Defect
The critical vulnerability identified in Atlassian Confluence, known as CVE-2023-22518, poses great danger to data security. The vulnerability lies in improper authorization which, if exploited, can result in significant data loss. This flaw is considered critical since it impacts all Confluence versions. Although the vulnerability cannot be exploited to exfiltrate data from affected Confluence servers, threat actors can exploit it to replace the state of an instance to attacker-supplied data, all without any authentication.
Preventive Measures and Updates
Atlassian has released Confluence Data Center and Server versions 7.19.16, 8.3.4, 8.4.4, 8.5.3, and 8.6.1 to tackle CVE-2023-22518. Atlassian advises all users to update their instances as soon as possible or, at the very least, create backups and restrict internet access to vulnerable instances until patches can be applied.
Response from Atlassian to Vulnerability Exploitation
Considering the serious nature of the vulnerability in the Confluence Data Center and Confluence Server, Atlassian moved promptly to address the issue. As immediate steps, Atlassian released patches for CVE-2022-26134 and rolled out a roster of updated server versions to curb exploits of the identified critical flaw, CVE-2023-22518.
Second Warning After Release of Patch
Less than five days after the release of the initial patch, Atlassian issued a second warning to its customers. The warning was necessitated because critical information relating to the vulnerability was made publicly accessible thereby elevating the risk of exploitation significantly.
Updated Confluence Data Center and Server Versions
In a proactive effort to mitigate the vulnerability, Atlassian released updated versions of Confluence Data Center and Server. Versions such as 7.19.16, 8.3.4, 8.4.4, 8.5.3, and 8.6.1 were released with measures embedded to address the CVE-2023-22518 issue. Furthermore, Atlassian alerted customers of an active exploit and pressed on the need for immediate action to secure their instances.
Guidance to Confluence Users
Amidst the ongoing risk associated with the CVE-2023-22518 vulnerability, Atlassian strongly advised its user base to either update their instances as soon as possible or introduce interim measures. As part of these interim measures, Atlassian suggested users create backups and block all internet access to vulnerable instances until they can apply the necessary patches. In addition, IP address safelisting rules implementation is recommended to further restrict access to Confluence. For users incapable of applying safelist IP rules to their Confluence server, the consideration of adding WAF protection is also recommended.
GreyNoise’s Analysis of the Confluence Vulnerability Exploitation
GreyNoise's threat intelligence scanners have been instrumental in monitoring and reporting on the active exploitation of the Confluence vulnerability coded as CVE-2023-22518. The company's vigilance has underscored the global span of this threat, tracking active exploit attempts across multiple countries.
In-the-Wild Exploitation of CVE-2023-22518
GreyNoise's scanners discovered clear signs of in-the-wild utilization of the CVE-2023-22518 vulnerability over a particular weekend. This discovery revealed relentless attempts by threat actors to capitalize on this vulnerability in their attacks.
Origin of Attacks Detected by GreyNoise
The analysis by GreyNoise further revealed that the exploitation attempts were originating from three distinct IP addresses. This indication of multiple points of origin underscores the widespread nature of the vulnerability's exploitation and further emphasizes the critical need for immediate mitigation strategies.
Impact of Confluence Vulnerability Exploitation
The exploitation of CVE-2023-22518 carries severe consequences, posing a significant threat to Confluence's Data Center and Server. Threat actors have found a way to replace the state of an instance with data of their own, without needing any form of authentication. This enables an attacker to interfere with the integrity of the data and the functions of the platform.
State Replacement without Authentication
The critical flaw of CVE-2023-22518 allows unauthorized access to internally stored data. Threat actors can manipulate this vulnerability to replace the state of an instance with attacker-supplied data, circumventing the need for authentication. This breach exposes organizations to potential data integrity issues and manipulation of critical applications.
Atlassian’s Warning on Active Exploitation
In the face of active exploitation, Atlassian issued a customer alert underscoring the immediate need for protective measures to be taken. The software company held that, once the patch is applied, no other action is required. In instances where the patch was not applied, an assumption of compromise should be made with immediate mitigation strategies put in place. Atlassian's warning also included the need to check for evidence of compromise, such as unexpected administrators, newly created user accounts, and particular requests in network access logs.




