Table of Contents
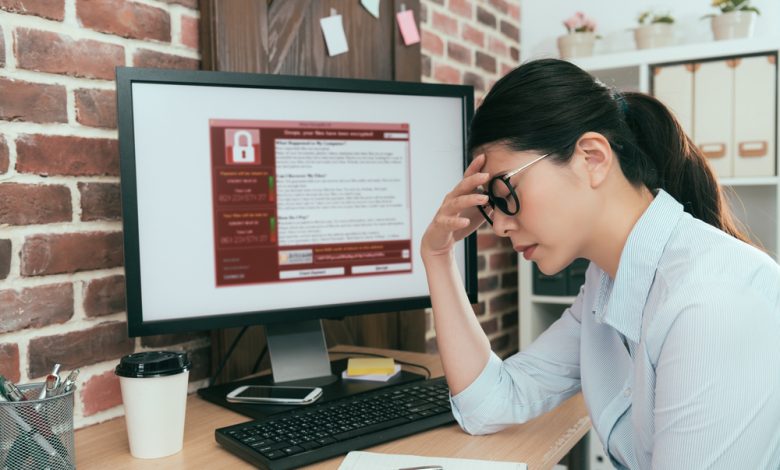
What is Ransomware?
Ransomware is a type of malware that prevents use of the computer system until a ransom has been paid, typically in the form of an electronic currency.
It can lock up all the files on a computer and usually demands payment to restore access.
How Does Ransomware Spread?
Ransomware may be propagated in the following ways:
1) using a trojan sold by hacker or created by authors of fake antivirus software, and then exploiting a vulnerability in your operating system to install it. The ransomware encrypts all data on the computer and forces victims to pay for the private key that is needed to unlock their data.
2) through spam e-mails, usually containing infected attachments or links to malicious programs. Once the ransomware is downloaded to your computer it locks up all your files with a strong encryption algorithm and displays its ransom note asking you for money in order for you get back access.
3) via infected websites hosting Ransomware. When you visit the website, the ransomware can infect your computer by either exploiting an already known vulnerability in your OS or an active vulnerability that is discovered by criminals.
How Does Apis Ransomware Work?
Apis Ransomware is a worm that is spread by exploiting vulnerable and unsecured network shares. Apis Ransomware spreads by exploiting an already known vulnerability in your operating system or an active vulnerability that is discovered by criminals. Apis Ransomware may also be propagated through spam e-mails, usually containing malicious links to the malicious program. Once you download Apis Ransomware on your computer, it locks up all your files with a strong encryption algorithm and displays its ransom note asking for payment in order for you to get back access.
Apis Ransomware has 3 variants which are named ApiTrojan, ApiPlanner2, ApiSapiens2. All 3 of these variants have the same ransom note and encryption process.
The malware contains 2 files, the executable program that does the encryption and decryption as well as a readme file that gives instruction to the victim on how to pay for the decryptor:
Protect your computer from being infected by all kinds of malicious programs, especially ransomware, with an advanced anti-malware software.
How to Remove Apis Ransomware
Remove the ransomware from your computer by following these steps:
Step 1) Scan the Computer. Download and install any anti-malware software on your computer. Scan the system for any malicious program you may have downloaded. This process usually takes some time and it is important not to interfere with it. Once scanning is done, allow the anti-malware software to remove all detected malicious files from your computer system.
Step 2) Disinfect Drive C:\ . You must start this step only if you have Apis Ransomware in this directory - C:\. Otherwise, skip this step and continue with Step 3). To disinfect drive C: follow these steps:
a) [ Start Windows Explorer and open C:\ ].
b) [ In the windows explorer, locate the drive you want to disinfect. Right-click on this drive and then click on "Properties". ]
c) Under "General" tab, click on "Folders" button.
d) Under "View" tab, make sure that under "Advanced Settings", all the checkboxes are selected for all the folders listed in table below:
e) Click OK to customize view settings. Saving changes will not remove this infection from your system.
Step 3) Delete Apis Ransomware.
a) Locate the malicious program. You can find it in C:\Program Files\Apis Technologies\ and/or in another folder you have not checked.
b) Locate the registry key [HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Apis Technologies]. Search for this key and remove all instances of the program from it.
c) Search your computer and delete all temp files, folders and registry keys you find with Apis Ransomware name.
d) Empty the Recycle Bin.
e) Run CCleaner to clean your system.
f) Restart your computer in normal mode. Your Windows should be now free of any file names like Apis Ransomware.
How to Protect My Computer From Ransomware
It is a best practice to keep your computer and devices protected with anti-malware software which can detect and remove malicious programs like ransomware. One of the best practices for protection against this type of malware is to avoid using email attachments or links that may seem benign, but are actually designed to install malware on your computer. Always be sure to validate or verify any links or attachments before opening them.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.