
A group of hackers using the Maze ransomware have released an extra 14GB of files that they claim were taken during an attack on Southwire in December. Southwire, a cable manufacturer from Georgia, had 120GB of data stolen from them in the attack. The data was released in response to their ransom demands not being met.
Table of Contents
The Trend of Targeting Big Organizations Continues
The cybercriminals behind the campaign demanded a ransom of $6m in exchange for the stolen files, which would be released if their demands weren't met. The company didn't respond, so the operators uploaded a portion of the data to a "News" site that was created to shame people who didn't pay up.
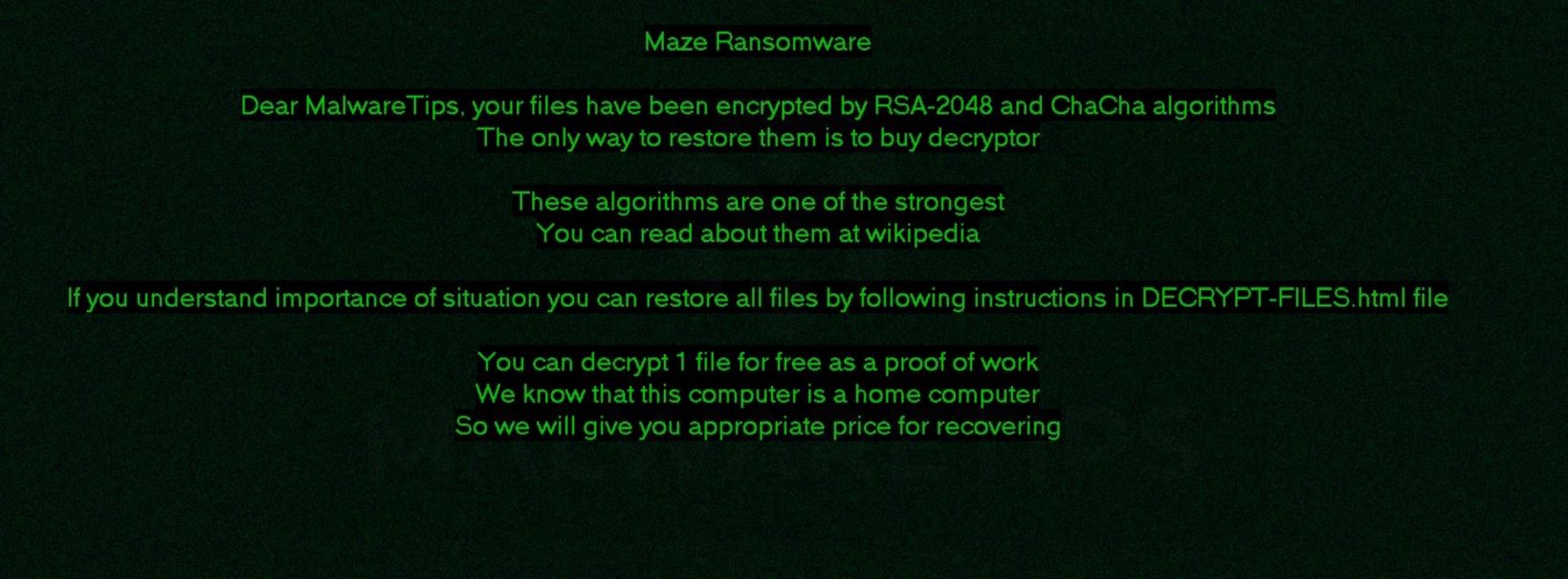
Figure 1.1: Maze Ransomware Note
Maze ransom note containing instructions on how victims should proceed to decrypt their files.
Southwire responded by filing a lawsuit against Maze and asking for an injunction on a web hosting provider that was hosting the news website Maze was running. The site was taken down, and the data was once again inaccessible.
Timed Data Leaks: The New Extortion Tactic
The Maze operators released a further 14.1GB of stolen data on a Russian hacking forum. They say that they will release a further 10% of the information for every week that the ransom goes unpaid. They made a post on the website saying;
"But now our website is back but not only that. Because of Southwire's actions, we will now start sharing their private information with you, this only 10% of their information and we will publish the next 10% of the information each week until they agree to negotiate. Use this information in any nefarious ways that you want."
Maze Ransomware - All your files, documents, photos, databases, and other important data are safely encrypted with reliable algorithms.
Maze Ransomware 2019 ‟Because we always give a second chance! ” pic.twitter.com/11ZsVnErfe
— CryptoInsane (@CryptoInsane) October 17, 2019
The threat actors said the release of the files isn't in response to the lawsuit taking down their website. They claim that this part of their scheme all along. The individual or group behind the Maze attack is using the release of the files as a negotiation tool to get the money that they want. Once they receive their payment, they will delete all the data they have and return it to Maze.
What Should a Company Do if Affected by Maze Ransomware?
Companies in this situation are advised never to pay the ransom. It encourages further hacks, and there's no telling if the hackers will keep their end of the bargain. Of course, it's not so easy to take that stance when you are actually in the situation.
Southwire has to weigh the potential costs of the information being released against the cost of paying the ransom. If that data contains third-party information, such as personal information on customers and employees, then the attack is considered a data breach.
If they were hit with a data breach, they would have to pay more for notifications to the people affected and government. They could also face potential fines over laws that could have been violated.
Given that the data is being released in small batches, each release of information would be classed as an individual data breach, meaning that each one is counted as one violation requiring one notification. The costs would quickly add up. It would behoove Southwire to act as soon as possible, no matter which action they choose to take.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.