Ragnar Locker Ransomware was first spotted in December 2019 as part of malware attacks against compromised networks. According to security researchers, this ransomware is specifically created not only to encrypt data but also to terminate installed programs (like ConnectWise and Kaseya) that are commonly used by managed service providers. Also, unlike other ransomware families, Ragnar Locker stops all running Windows services before encrypting victims' files.
Table of Contents
How Does Ragnar Locker Ransomware Infect Computers
Ragnar Locker is distributed via spam campaigns, fake software updaters, unofficial software activation tools, untrustworthy software download channels, and Trojans.
- Spam campaigns - Attackers send emails with malicious attachments (or web links that download malicious files) in them. Usually, hackers attach files like Microsoft Office, PDF documents, archive files, executable files, or JavaScript files. Once the victims open these files, Ragnar Locker will be installed on their computers.
- Fake software updaters – They infect systems either by exploiting flaws of outdated programs installed on a targeted machine or by installing malicious software instead of legitimate updates. Untrustworthy sources for software download could be Peer-to-peer networks, freeware download, third party downloaders, free file hosting web pages, etc. Hackers use them as tools to host malicious files disguised as legitimate files. When downloaded and opened, they infect victims' computers with malicious software.
- Software 'cracking' tools - some people use unofficial programs to bypass paid activation of licensed software. Unfortunately, these tools are dangerous as hackers often use them for distributing malware.
- Trojans - cybercriminals are well aware that if installed onto a system, trojans can cause severe chain infections. For that reason, hackers often use programs of this type for installing malware.
Services Targeted by Ragnar Locker Ransomware
Before encrypting users' data, Ragnar Locker disables all of the running Windows services on their computers. Services that contain certain strings are also immediately terminated.
The list of targeted strings is shown below:
- vss
- sql
- memtas
- mepocs
- sophos
- veeam
- backup
- pulseway
- logme
- logmein
- connectwise
- splashtop
- kaseya
Ragnar Locker Ransomware Encryption Process
Before deploying Ragnar Locker Ransomware on a targeted machine, cybercriminals will perform reconnaissance and some pre-deployment tasks such as stealing the victim's sensitive data. After stealing it, the attackers will upload the data to their servers demanding a ransom payment for releasing it.
Once the targeted machine has been prepped for encryption, Ragnar Locker will begin to encrypt the files on it. The ransomware doesn’t encrypt every file on a computer. It avoids files in the following folders, and with the following file names and extensions:
- kernel32.dll
- Windows
- Windows.old
- Tor browser
- Internet Explorer
- Opera
- Opera Software
- Mozilla
- Mozilla Firefox
- $Recycle.Bin
- ProgramData
- All Users
- autorun.inf
- boot.ini
- bootfont.bin
- bootsect.bak
- bootmgr
- bootmgr.efi
- bootmgfw.efi
- desktop.ini
- iconcache.db
- ntldr
- ntuser.dat
- ntuser.dat.log
- ntuser.ini
- thumbs.db
- .sys
- .dll
- .lnk
- .msi
- .drv
- .exe
In this video, the Huntress team shows how Ragnar Locker ransomware kills MSPs before commencing the encryption process.

The ransomware appends a new file extension, like .ragnar_22015ABC, to the file's name. The 'RAGNAR' file marker will also be added to the end of every encrypted file.
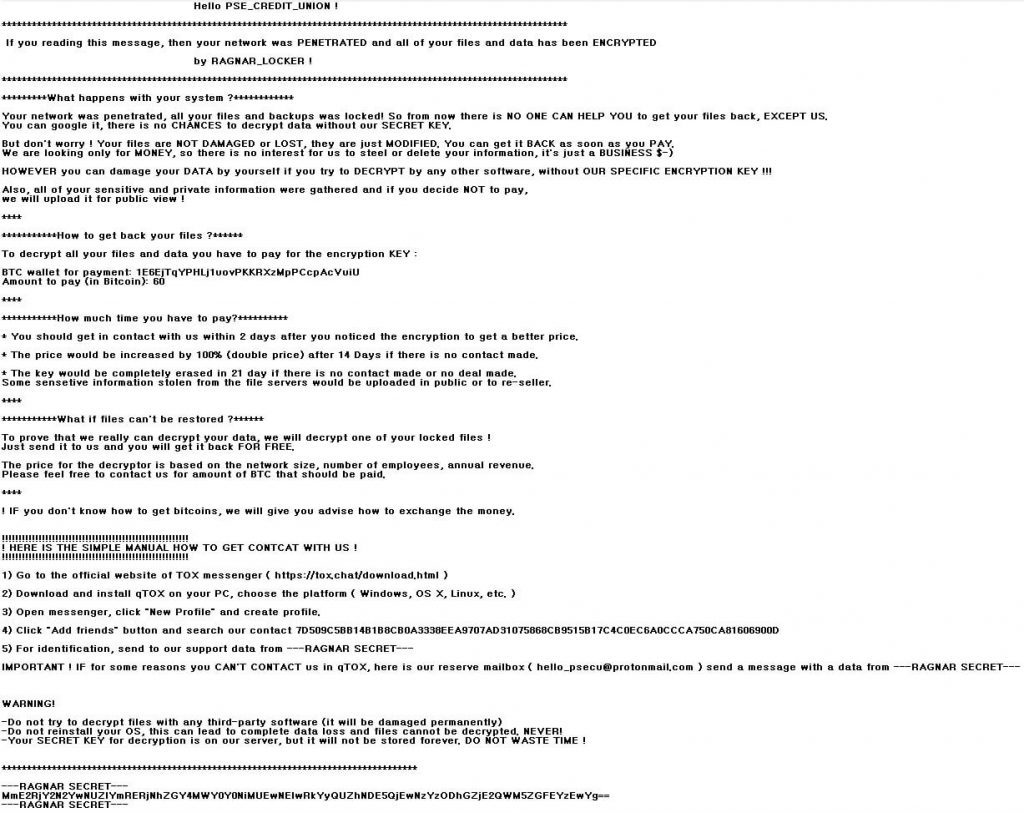
Finally, Ragnar Locker will drop a ransom note named ‘.RGNR_[extension].txt.’ The ransom note contains information on the ransom amount, a bitcoin payment address, a TOX chat ID to communicate with the cybercriminals, and a backup email address if TOX does not work. In each case, the ransom amount is calculated individually. According to reports, the amount of the ransom varies between $200,000 to $600,000.
Figure 2: Image: Ragnar Locker Ransom Note
A ransom note generated by Ragnor Locker. The victim in this case seems to be a credit union given the hackers' greeting to "PSE_CREDIT_UNION." Source: https://sensorstechforum.com/
Victims of Ragnar Locker are warned that if they do not contact the ransomware developers within 14 days of encryption, the price of decryption tools will be doubled, and after 21 days the decryption key will be deleted permanently. Also, if the ransomware victims do not contact Ragnar Locker's creators at all, their sensitive data could be uploaded to public servers or sold to third parties.
Precautions Against Ragnar Locker Ransomware
At this point, it is not known whether hackers are actually stealing sensitive data before encrypting victims' files. However, considering the common tactic with enterprise-targeting ransomware, Ragnar Locker attacks aren’t about to stop any time soon. For that reason, users should have data backups and be extra careful when browsing the web to keep their computers safe from malware.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.