
Researchers observed a new IoT (Internet of Things) botnet called Ttint targeting Tenda routers. Security researchers at NetLab report that the botnet uses a malware threat that exploits two zero-day vulnerabilities to infect its targets.
Ttint not only performs DDoS attacks to infect its target but also implements 12 additional remote access techniques to attack routers, employs routers as traffic proxies, and tempers with the routers' DNS and firewall settings. Additionally, the threat allows its operators to execute commands on the host devices.
Two Unpatched Zero-Day Vulnerabilities Used in Ttint Campaigns
NetLab reports that the Ttint malware was first deployed last year. Researchers detected Ttint in November 2019.Ttint targeted vulnerable Tenda routers by exploiting the CVE-2020-10987 vulnerability, which was first disclosed on July 10, 2020.
The attacks continued till July 2020, when Sanjana Sarda, a researcher at Independent Security Evaluators, published a detailed report about the five vulnerabilities, one of which being CVE-2020-10987.
Despite the warning, Tenda didn't release a security patch. Ttint, on the other hand, didn't waste time waiting for Tenda to interfere with their activities. A few weeks after Sarda published the report, Ttint started abusing a second zero-day vulnerability in Tenda routers.
Figure1: Ttint Attack Vector
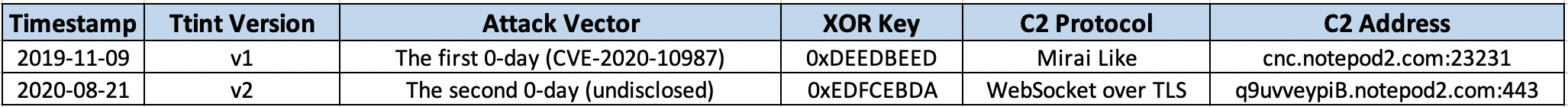
NetLab didn't publish details about the zero-day vulnerabilities due to security concerns. However, the researchers reached out to Tenda, who are yet to address the security concerns.
According to the research, Tenda routers running firmware versions AC19 to AC18 are vulnerable. Researchers say that the attackers could redirect unsuspecting Tenda users to malicious websites by altering the DNS settings of their vulnerable routers.
Therefore, users are recommended not to use unpatched routers. Users who are unsure whether their devices are vulnerable can check the firmware version in the router's admin panel.
About Ttint Malware
Ttint is a Remote Access Trojan (RAT) based on the code of another infamous botnet malware called Mirai, which was leaked in 2016.
Ttint behaves like a standard botnet while running. It deletes its files and prevents the host device from restarting. The threat also implements typical Mirai features, such as running as a single instance by binding the port, selecting random process names, and integrating a large number of attack vectors.
Although other similar versatile threats were observed in the past, this level of adaptable RAT has never been used to attack IoT devices. Ttint could be the first of a new generation IoT malware, deployed in sophisticated campaigns.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.