
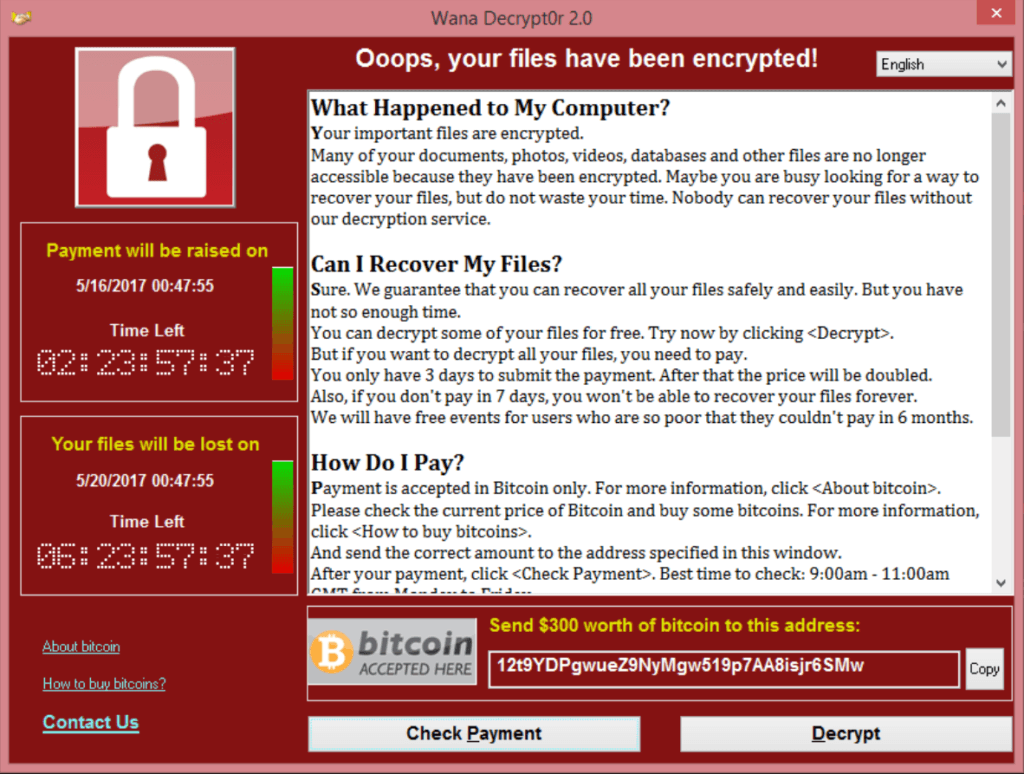
The NSA dropped the ball a couple weeks ago when millions became victims in the WannaCry ransomware attack. The infection, which was developed by the United States Government and specifically the National Security Agency (NSA) was compromised and as a result of getting into the wrong hands, wreaked havoc on Americans from coast to coast.
One legislator in DC is attempting to get in front of any potential recurrences of this type of problem. A new bill introduced by Sen. Brian Schatz (D-HI), would establish better protocols and help bring accountability to how the NSA deals with any vulnerabilities. The Protecting Our Ability to Counter Hacking Act of 2017, or PATCH Act, would look to establish a legal framework for the process and requires federal agencies to establish policies on when to share vulnerabilities and, if unclassified makes those policies widely available to the public.
Although Microsoft has issued a patch in March to prevent this issue from affecting users many had failed to update their systems. The majority of affected users, roughly 98 percent, were running some version of Microsoft Windows 7, with less than one in a thousand running some version of Microsoft Windows XP. 2008 R2 Server clients also were among the affected, making up just over 1% of infections.
Global Map of Infection:
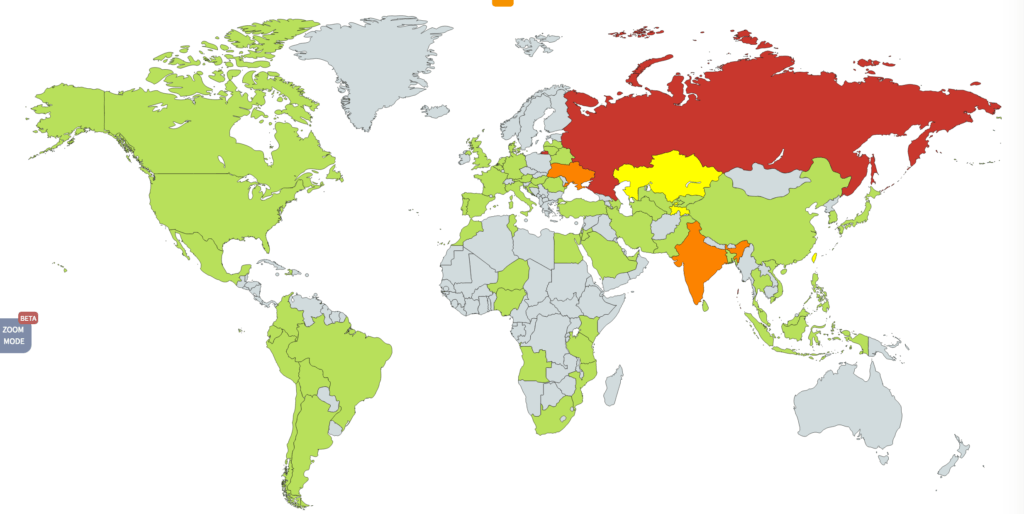
Windows 7 is still very popular as it is on 4 times as many computers as Windows 10. The newer operating systems were prepared and less vulnerable and that was evident in the damage reporting.
The issue of these infections getting in the wrong hands comes into play as our dicey foreign policy situation with poorer and technologically disadvantaged countries like North Korea is considered. While lacking in military and technological might these infections provide the ability to stifle and otherwise be a nuisance to other countries. Kim Jong Un is a dictator starving for attention and who’s behavior is similar to a petulant child. The potential disruption he can use this type of technology for can be used as an avenue to relevance for his struggling regime.
In any event, the important thing will be how the American government deals with securing its developed and proprietary technology going forward. This recent attack was a major costly failure with ramifications yet to be seen and understood. While many are lauding Sen. Schatz’s bill, will it be enough? Are we spending too much on the development of and protection of this type of technology or too little?
Has the US Government identified and protected its networks sufficiently in the wake of event or are we just waiting for the next major computerized calamity? Share your opinion in the comments section below.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.