Researchers at security company Imperva published a two-part analysis of a new Botnet called KashmirBlack that exploits CMS Platforms, such as WordPress, Joomla!, Drupal, Vbulletin, PrestaShop, Magneto, OpenCart, OsCommerence, and Yeager.
DevOps, the criminal organization behind KashmirBlack, has put together a robust infrastructure that runs the botnet operations smoothly with minimal interruptions. The malicious network has spread to over 30 countries worldwide since it was first spotted in late 2019,
The infrastructure has one C&C (Command and Control) server and uses more than 60 surrogate servers that handle hundreds of bots tasked to expand the network by performing brute-force attacks.
KashmirBlack botnet is currently used for crypto mining, spam spreading, and website defacement attacks.
Table of Contents
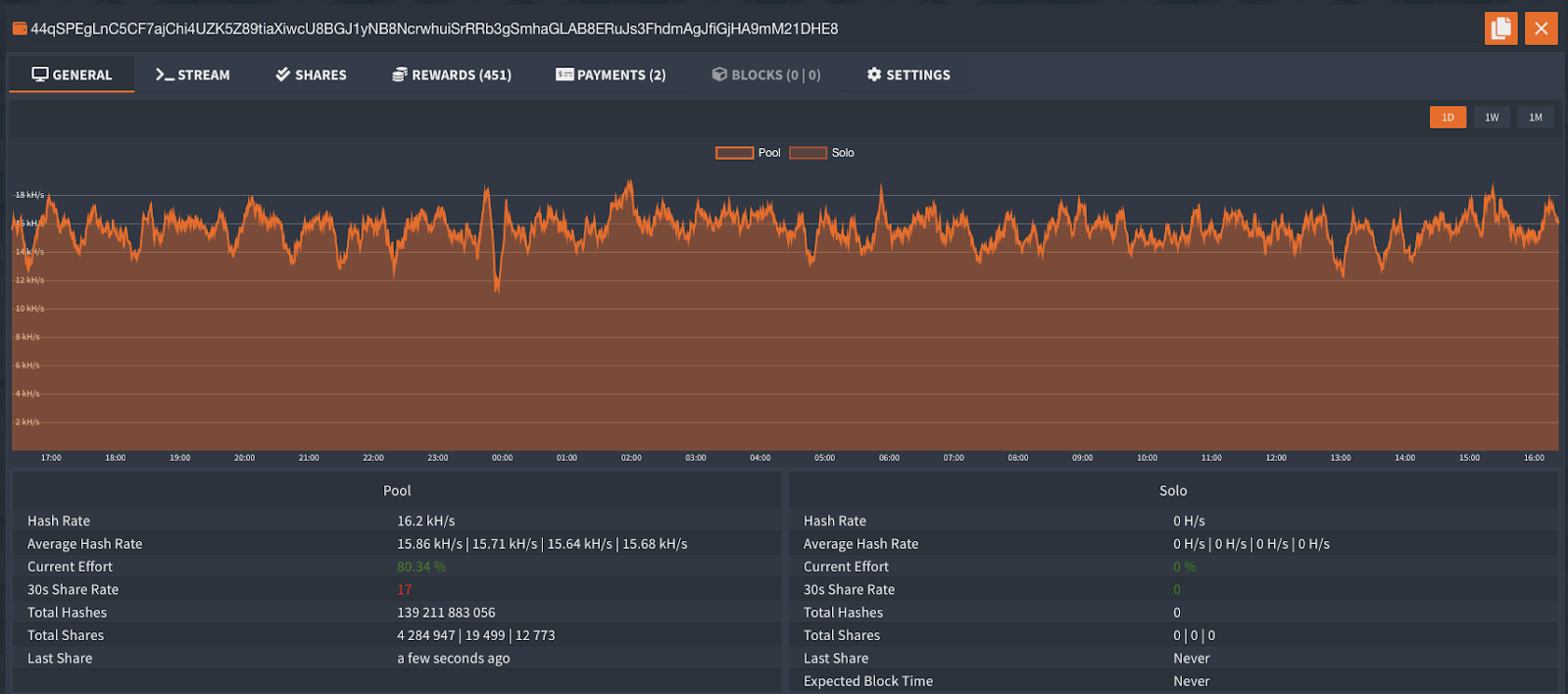
Monero Crypto Mining
KashmirBlack botnet uses the popular XMRig miner to mine Monero cryptocurrency. Researchers calculated that since the start of the mining operation on March 31, 2020, around 80 infected victim hosts were dragged into the crypto mining campaign.
Figure 1 Mining Flow
Spamming
To investigate the botnet's activity, Imperva researchers created a CMS honeypot, which was converted into a spamming bot. The experiment revealed that when a visitor attempts to access the honeypot's login page, they would be redirected to a server, which will perform additional redirection to a random clickbait website.
Researchers point out that KashmirBlack is very adaptable. The attackers can easily change the targets and objectives of the botnet by making small changes to the infrastructure.
The research reveals that every component in the botnet is independent and can be easily replaced by another.
Exploited Vulnerabilities
The KashmirBlack botnet operation, as we know it now, started with the exploitation of a PHPUnit RCE vulnerability (CVE-2017-9841), which was used to infect customers with a malicious KashmirBlack script.
While the CVE-2017-9841 vulnerability is exploited to turn victims into spreading bots, another 15 flaws in CMS systems are utilized to convert sites into pending bots.
Additional WebDAV file upload vulnerability allows attackers to deface websites, a form of cyberattack that changes the visual appearance of the target webpage.
Interestingly, last month, the researchers observed KasmirBlack using Dropbox as a replacement for its C&C infrastructure, abusing the cloud service's API to fetch attack instructions and upload reports from the spreading bots.
"Moving to Dropbox allows the botnet to hide illegitimate criminal activity behind legitimate web services," Imperva said.
By migrating the C&C operation to a cloud service, the threat operators demonstrate a determination to camouflage their malicious network so that it will continue its operations in the future.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.