
Microsoft Security Intelligence issued a series of tweets warning of an ongoing phishing campaign that targets companies with a weaponized variant of the NetSupport Manager remote administration application.
According to the tech giant, since it was first detected on May 12, the massive COVID-19-themed phishing campaign has used “several hundreds of unique attachments.” The criminals behind the attack use a plethora of deceptive messages, some of which pretend to be sent from the Johns Hopkins Center.
In one of the most recent variants of the campaign, the attackers use deceptive emails that pose as an official update on the number of COVID-19 deaths in the US. The emails contain a malicious Excel file named covid_usa-nyt-8072.xls, which, when opened, will display fabricated data and will urge the victim to “Enable Content.” If the victim falls into the trap of enabling macros, malicious Excel 4.0 macros will download and save the NetSupport Manager RAT as “dwm.exe” in a random folder named “%appdata%.” The use of a “fake” APPDATA folder is a simple but clever trick, which will hide the malware from users who check the Task Manager.
Figure 1: Screenshot of the malicious covid_usa-nyt-8072.xls file
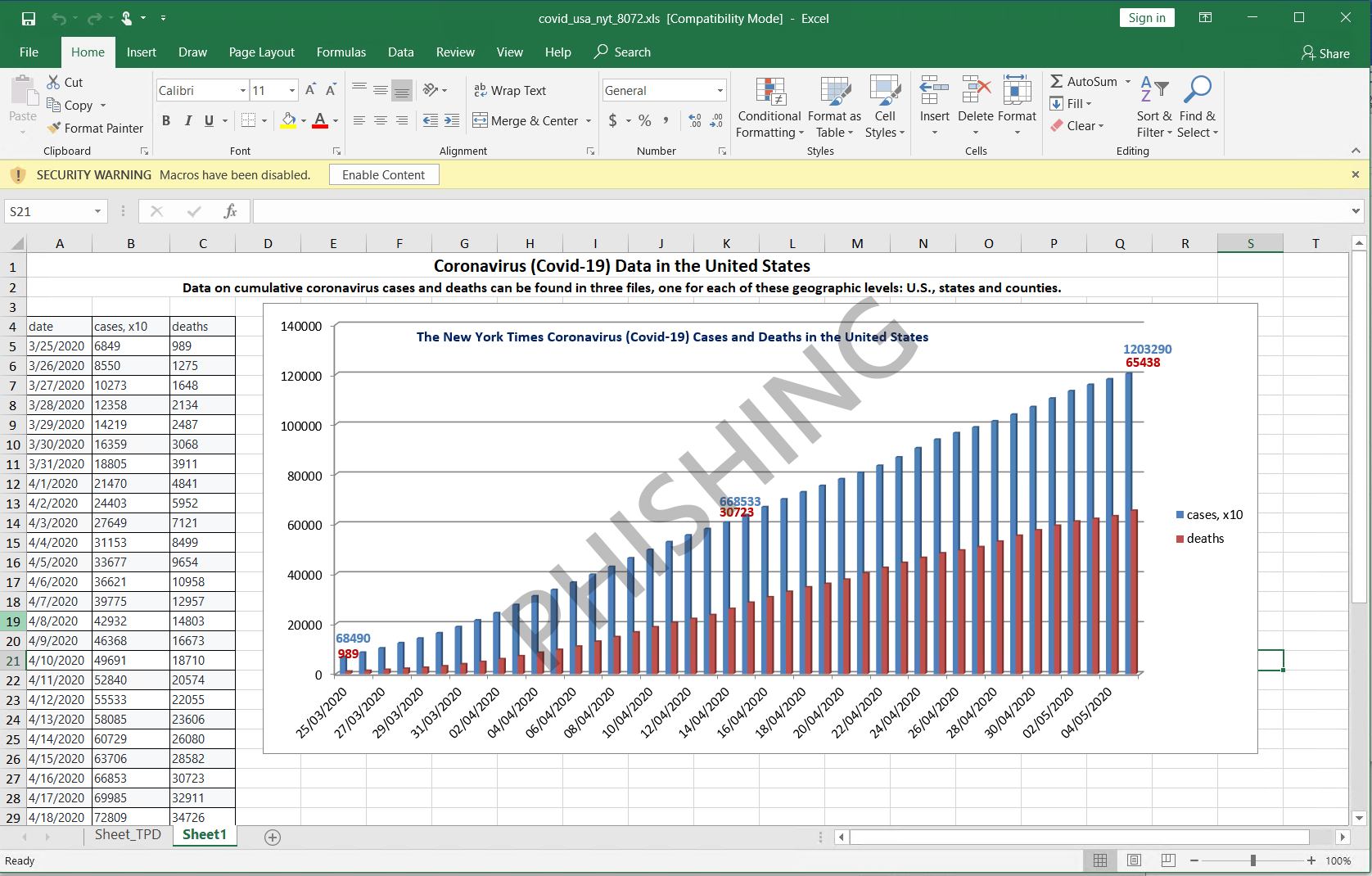 In this image, we can see the malicious Excel document to ask the user to “Enable Content.” Source: Twitter
In this image, we can see the malicious Excel document to ask the user to “Enable Content.” Source: Twitter
Johns Hopkins Center also published a warning in response to the Microsoft alerts, informing their followers that their daily updates don’t contain attachments and urging them to be more cautious.
What is NetSupport Manager RAT?
NetSupport Manager is a legitimate remote access tool (RAT) that is advertised as a remote administration tool used for troubleshooting. However, the software is often abused by cybercriminals who use it as a remote access trojan.
In past campaigns, the RAT was spread through elaborate schemes using a range of lures. NetSupport Manager RAT was used as an information-stealer in a recent phishing campaign from February 2020. The criminals used a password-protected MS Word document to lull their victims into a false sense of security. Once the victim entered the password, malicious macros downloaded the RAT and compromised the device.
It is not uncommon for attackers to use passwords and other similar tricks to gain their victims’ trust. Many NetSupport Manager RAT campaigns utilized various schemes, such as fake updates and malicious pop-ups, to deliver the dangerous threat. One way or another, the interaction with malicious content leads to a nasty computer infection.
Microsoft warns that NetSupport Manager is likely to infect the compromised devices with other malware. Once installed, the RAT will connect to a remote command and control (C&C) server, which allows the attackers to control the RAT, potentially instructing it to install additional threats.
“The NetSupport RAT used in this campaign further drops multiple components, including several .dll, .ini, and other .exe files, a VBScript, and an obfuscated PowerSploit-based PowerShell script. It connects to a C2 server, allowing attackers to send further commands,” - Statement by Microsoft
The remote administration tool gives the attackers full control of the compromised device, allowing them to execute commands, exfiltrate sensitive information, and corrupt user files. Users who suspect potential infection with NetSupport Manager RAT are advised to take prompt action and scan their devices with a reliable antimalware tool. It is recommended that users should go through accounts and change compromised passwords following this system cleanup.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.