Microsoft Security Intelligence issued a series of tweets warning of a new ransomware family named PonyFinal. The threat, which is a Java-based cryptolocker, was deployed in human-operated attacks that target corporate networks.
Unlike most ransomware operators who use automated processes to reach a vast number of victims, the gang behind PonyFinal carefully chooses their victims. PonyFinal has attacked very few victims since it was first discovered earlier this year. PonyFinal has been detected in India, Iran, and the US.
Microsoft adds that PonyFinal is one of several human-operated ransomware strains that has taken advantage of the COVID-19 pandemic to repeatedly target the healthcare sector.
Table of Contents
How PonyFinal spreads
According to Microsoft, the criminals behind PonyFinal tend to breach corporate networks by using brute-force attacks to guess weak passwords. Once inside, Visual Basic scripts will run PowerShell reverse scripts to dump data. Additionally, the attackers will deploy "a remote manipulator system," which, according to Microsoft, will bypass event logging.
Since PonyFinal is written in Java, Java Runtime Environment (JRE) is needed for the ransomware to run. Usually, the attackers steal information from the system management server to detect and target systems that have JRE installed. However, researchers observed the hackers will install JRE on devices that don't have the environment installed.
The final payload of the ransomware is delivered by a .MSI file that also contains two additional batch files. A file named UVNC_Install.bat will create a scheduled task named "Java Updater" and will call RunTask.bat, which will run the ransomware payload, PonyFinal.JAR.
Figure 1: Attack chain
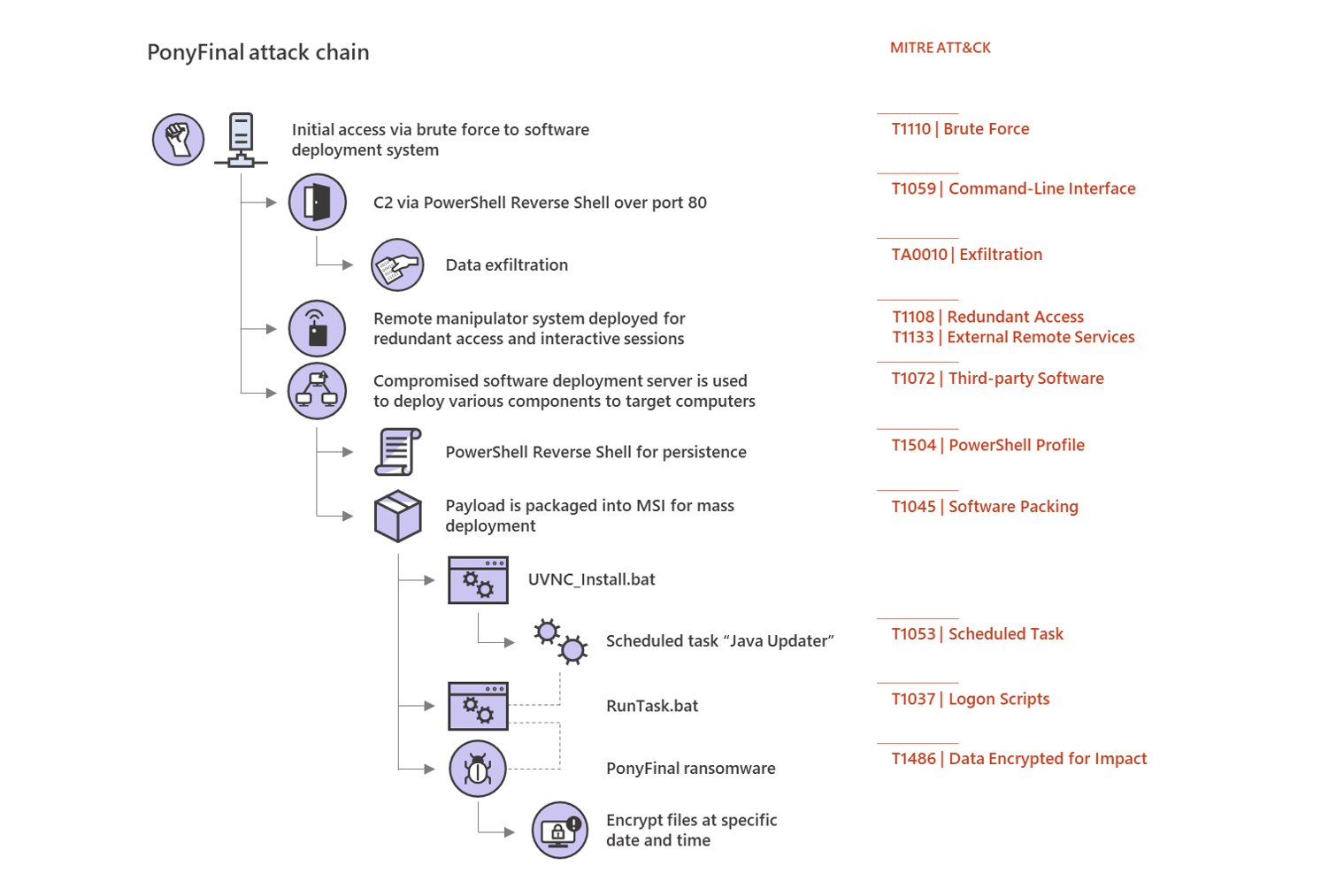 This image illustrates PonyFinal’s infection mechanism. Source: Twitter
This image illustrates PonyFinal’s infection mechanism. Source: Twitter
PonyFinal establishes persistence by using PowerShell commands to launch mshta.exe (a system tool) and set up a reverse shell, based on a common PowerShell attack framework. Microsoft adds that the attackers were also observed to use legitimate tools, such as Splashtop, to maintain a remote connection.
Researchers warn that once the attackers have an established presence on a device, they will attempt to compromise other devices connected to the local network.
File encryption
According to Microsoft, the attackers can select a specific date and time for the file encryption to begin. PonyFinal will add the ".enc" extension at the end of each corrupted file. For example, a document named example.txt will get renamed to example.txt.enc.
The ransomware will also drop a ransom note, a file named README_files.txt, which informs the victim of their situation and demands a hefty ransom of 300 BitCoin, to be paid within 72 hours. It is not unusual for threat actors to give their victims tight deadlines. Victims are more likely to act impulsively and irrationally when they feel pushed. The threat actors further influence their victims by promising to decrypt up to 3 files for free. This creates a false sense of trust in the victim, who comes to take the attacker at their word.
Ransom note:
Dear [XXXXX],
All your important files were encrypted on all computers.
You can verify this by click on see files an try open them.
Encryption was produced using unique KEY generated for this computer.
To decrypted files, you need to obtain private key.
The single copy of the private key, with will allow you to decrypt the files, is locate on a secret server on the internet;
The server will destroy the key within 72 hours after encryption completed.
Pay us 300 BTC , and we will decode upto 3 sample files you send us via email for verification to prove we deliver master key, send file sample to: thecurelegion@protonmail.com
Bitcoins have to be sent to this address: 3JKX3VWDPW7gvVaXFVv3UazY29pE2LGV7b
After you’ve sent the payment send us an email to : thecurelegion@protonmail.com with subject : Decryption of files
If you are A not familiar with bitcoin you can buy it from here :
SITE : www.localbitcoin.com
After we confirm the payment , we send the private key so you can decrypt your system.
Sadly, there is no third-party decryption tool for PonyFinal's lock. However, paying the ransom is not advisable as doing that will only encourage the criminals to continue their malicious activities.
Conclusion
According to Microsoft, PonyFinal is a part of an online set of ransomware campaigns that are likely to remain dormant. Multiple ransomware groups have been accumulating network access and maintaining persistence on target networks. The researchers report that dozens of new deployments went live at once in the first weeks of April.
Ransomware such as Sodinokibi, Ryuk, NetWalker, and Bitpaymer have been deployed in massive attacks that targeted not only the business but also the healthcare sector. As the ransomware operators have no regard for the critical services they attack, the researchers warn that organizations should be vigilant and pay heed to the little warning signs, such as credential theft and unexpected activities related to security logs and tools, as well as penetration-testing tools.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.