
Silvertor ransomware is a dangerous piece of malware that was found by the ransomware hunter Karsten Hahn. This threat is known for restricting data access for its victims’ by encrypting their files and demanding a ransom payment in Bitcoin cryptocurrency for their recovery. The data-encoding ransomware uses a powerful encryption algorithm to lock users’ data making it completely inaccessible. According to malware researchers, Silvertor ransomware is considered dangerous as infection could lead to infections of other malware and permanent data loss.
Table of Contents
How is Silvertor Ransomware Distributed
Similar to other ransomware infections, Silvertor is often distributed via spam emails that contain malicious attachments, by exploiting vulnerabilities in the operating system or installed software, or through malvertising.
The attackers would send an email with fake header information, luring the victims to believe that it is from a shipping company or another familiar institution. For instance, the email from the shipping company informs them that a courier attempted to deliver a parcel, but failed. Sometimes the spam emails pretend to be notifications of a shipment that victims have made. In any case, the only way to see what the email is referring to is to open the attached file or click on a link embedded inside the spam email. Once the victims do that, their computers will be infected with Silvertor ransomware.
Another way Silvertor is being distributed is by exploiting software installed on a targeted machine, or by operating system vulnerabilities. Usually, the exploited programs include the operating system itself, web browsers, Microsoft Office, and third-party applications.
Silvertor ransomware can also be distributed via malvertising. Therefore, users should never click on suspicious adverts that they encounter when surfing the Internet. Users should also consider installing an ad blocker to prevent advertising in the future.
How Does Silvertor Ransomware Work
Silvertor ransomware attacks all versions of Windows and, once installed on the system, the malware starts scanning all the drives on the computer to search for files to encrypt.
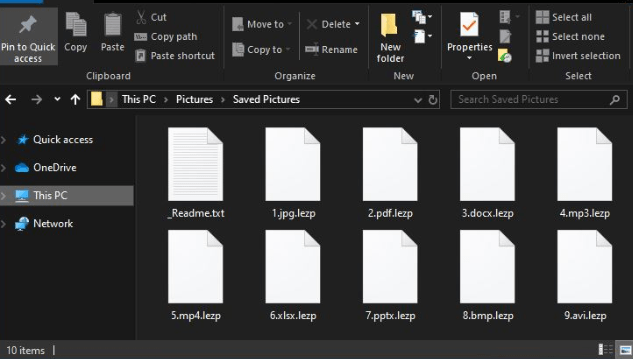
The data encrypted by Silvertor ransomware includes important documents, photos, videos and files such as .doc, .docx, .xls, .pdf, etc. When detected, the ransomware adds the ".silvertor" extension to each of them, and users are no longer able to open them. For example, a file named "1.jpg" would appear as "1.jpg.silvertor" following the encryption.
Figure1: Files Encrypted by Silvertor Ransomware
Encrypted files appended with the ".silvertor" extension. Source: 2 Remove Virus
After the encryption process is complete, Silvertor ransomware drops a "README.html" ransom note on the desktop and in each folder that contains encrypted files. The ransom note offers the victim the chance to decrypt their files in exchange for a Bitcoin payment.
The ransom note states that all users’ personal files are encrypted by Silvertor ransomware and can only be decrypted by using a valid decryption tool offered by the malware authors. To get this tool, the victims should write an email to the hackers. The developers will reply to the victim with their demanded ransom fee alongside other details that explain how the users can pay the sum.
The ransom is $250 in Bitcoin and it must be paid within the first 10 hours as, once the deadline is passed, the victims’ files will be rendered undecryptable.
Unfortunately, in many cases, users do not receive the decryption tools despite paying the ransom fee. Therefore, security experts say victims should NOT pay the ransom to prevent financial loss.
How to Remove Silvertor Ransomware
Removing malware threats by yourself might be very dangerous as you risk losing your important data for good. For that reason, you should look for expert advice and contact the following government fraud and scam websites to report for the ransomware attack:
- In the United States, go to the On Guard Online website.
- In Australia, go to the SCAMwatch website.
- In Canada, go to the Canadian Anti-Fraud Centre.
- In France, go to the Agence nationale de la sécurité des systèmes d’information
- In the United Kingdom, go to the Action Fraud website.
- In Germany, go to the Bundesamt für Sicherheit in der Informationstechnik website.
- In Ireland, go to the An Garda Síochána website.





Leave a Reply
Thank you for your response.
Please verify that you are not a robot.